Authenticating and Authorizing Microsoft Azure Active Directory Users for Oracle Databases
An Oracle Database instance can be configured for Microsoft Azure AD users to connect using Azure OAuth2 access tokens.
- Introduction to Authorizing Microsoft Azure AD Users for an Oracle Database
Before you begin authenticating and authorizing Microsoft Azure AD users for an Oracle Database, you should understand the overall process. - Configuring the Oracle Database for Microsoft Azure AD Integration
The Microsoft Azure AD integration with the Oracle Database instance requires the database to be registered with Azure AD so that the database can request the Azure AD public key. - Mapping Oracle Database Schemas and Roles
Azure AD users will be mapped to one database schema and optionally to one or more database roles. - Configuring Azure AD Client Connections to the Oracle Database
You can configure client connections to connect with the Azure AD registered database - Trace Files for Troubleshooting Oracle Database Client Connections with Azure AD
You can use trace files to troubleshoot Oracle Database client connections with Azure AD connections.
Parent topic: How-to Guides
Introduction to Authorizing Microsoft Azure AD Users for an Oracle Database
Before you begin authenticating and authorizing Microsoft Azure AD users for an Oracle Database, you should understand the overall process.
- About Authorizing Microsoft Azure AD Users for an Oracle Exadata Database Service on Dedicated Infrastructure
Users for Oracle Exadata Database Service on Dedicated Infrastructure can be centrally managed in a Microsoft Azure Active Directory (Azure AD) service. - Azure AD Users Mapping to an Oracle Database Schema and Roles
Microsoft Azure users must be mapped to an Oracle Database schema and have the necessary privileges (through roles) before being able to authenticate to the Oracle Database instance. - Use Cases for Connecting to an Oracle Database Using Azure AD
Oracle Database supports four types of use cases for connecting to an Oracle Database instance using Microsoft Azure Active Directory. - General Process of Integrating Microsoft Azure AD with Oracle Exadata Database Service on Dedicated Infrastructure
Both the Oracle and the Microsoft Azure administrators play roles in configuring the connection between Oracle Exadata Database Service on Dedicated Infrastructure and Microsoft Azure AD.
About Authorizing Microsoft Azure AD Users for an Oracle Exadata Database Service on Dedicated Infrastructure
Users for Oracle Exadata Database Service on Dedicated Infrastructure can be centrally managed in a Microsoft Azure Active Directory (Azure AD) service.
You can perform this integration in the following Oracle Database environments:
- On-premises Oracle Database release 19.16 and later, but not for Oracle Database 21c
- Oracle Exadata Database Service on Dedicated Infrastructure on Database versions 19.17 and later. This feature is not supported on Oracle Database release 21c.
- Oracle Base Database Service
The instructions for configuring Azure AD use the term "Oracle Database" to encompass these environments.
This type of integration enables the Azure AD user to access an Oracle Exadata Database Service on
Dedicated Infrastructure instance. Azure AD users and applications can log in with Azure AD Single Sign On (SSO) credentials to get an Azure AD OAuth2 access token to send to the database.
The administrator creates and configures the application registration (app registration) of the Oracle Exadata Database Service on Dedicated Infrastructure instance with Azure AD. The database administrator also creates application (app) roles for the database app registration in Azure AD, and assigns these roles to Azure AD users, groups, and applications. These app roles will be mapped to the database global schemas and global roles. An Azure AD principal that is assigned to an app role will be mapped to either a database global schema or database global role. An Oracle global schema can also be mapped exclusively to an Azure AD user. When the principal is a guest user or service principal, they can only be mapped to the database schema through an Azure app role. An Oracle global role can only be mapped to an Azure app role.
Tools and applications that are updated to support Azure AD tokens can authenticate users directly with Azure AD and pass the database access token to the Oracle Exadata Database Service on
Dedicated Infrastructure instance. You can configure existing database tools such as SQL*Plus to use an Azure AD token from a file location. In these cases, Azure AD tokens can be retrieved using tools like Microsoft PowerShell or Azure CLI and put into a file location. An Azure AD OAuth2 database access token is a bearer token with an expiration time. The Oracle Database client driver will ensure that the token is in a valid format and that it has not expired before passing it to the database. The token is scoped for the database. Assigned app roles for the Azure AD principal are included as part of the access token. The directory location for the Azure AD token should only have enough permission for the user to write the token file to the location and the database client to retrieve these files (for example, just read and write by the process user). Because the token allows access to the database, it should be protected within the file system.
Azure AD users can request a token as a client registered with Azure AD app registration by using methods such as the following:
- Passing the Azure AD user name and password through a command line, script, file, or any other supported method
- Entering the Azure AD credentials into an Azure AD authentication screen with or without multi-factor authentication
Oracle Exadata Database Service on Dedicated Infrastructure supports the following Azure AD authentication flows:
- Resource owner password credential (ROPC), which is used in non-graphic user interface environments when a pop-up window cannot be used to authenticate a user.
- Authorization code, which is used when a browser can be used to enter credentials for the user
- Client credentials, which are for applications that connect as themselves (and not the end-user)
- On-Behalf-Of (OBO), where an application requests an access token on behalf of a logged-in user to send to the database
Oracle Exadata Database Service on Dedicated Infrastructure accepts tokens representing the following Azure AD principals:
- Azure AD user, who is registered user in the Azure AD tenancy
- Guest user, who is registered as a guest user in the Azure AD tenancy
- Service, which is the registered application connecting to the database as itself with the client credential flow (connection pool use case)
Azure AD Users Mapping to an Oracle Database Schema and Roles
Microsoft Azure users must be mapped to an Oracle Database schema and have the necessary privileges (through roles) before being able to authenticate to the Oracle Database instance.
In Microsoft Azure, an Azure AD administrator can assign users, groups, and applications to the database app roles.
Exclusively mapping an Azure AD schema to a database schema requires the database administrator to create a database schema when the Azure AD user joins the organization or is authorized to the database. The database administrator must also modify the privileges and roles that are granted to the database schema to align them with the tasks the Azure AD user is assigned to. When the Azure AD user leaves the organization, the database administrator must drop the database schema so that an unused account is not left on the database. Using the database app roles enables the Azure AD administrator to control access and roles by assigning users to app roles that are mapped to global schemas and global roles. This way, user access to the database is managed by Azure AD administrators and database administrators do not need to create, manage, and drop schemas for every user.
An Azure AD user can be mapped to a database schema (user) either exclusively or through an app role.
- Creating an exclusive mapping between an Azure AD user and an Oracle Database schema. In this type of mapping, the database schema must be created for the Azure AD user. Database privileges and roles that are needed by the Azure AD user must be granted to the database schema. The database schema not only must be created when the Azure AD user is authorized to the database, but the granted privileges and roles must be modified as the Azure AD roles and tasks change. Finally, the database schema must be dropped when the Azure AD user leaves the organization.
- Creating a shared mapping between an Azure AD app role and an Oracle Database schema. This type of mapping, which is more common than exclusive mappings, is for Azure AD users who have been assigned directly to the app role or is a member of an Azure AD group that is assigned to the app role. The app role is mapped to an Oracle Database schema (shared schema mapping). Shared schema mapping allows multiple Azure AD users to share the same Oracle Database schema so a new database schema is not required to be created every time a new user joins the organization. This operational efficiency allows database administrators to focus on database application maintenance, performance, and tuning tasks instead of configuring new users, updating privileges and roles, and removing accounts.
In addition to database roles and privileges being granted directly to the mapped global schema, additional roles and privileges can be granted through mapped global roles. Different Azure AD users mapped to the same shared global schema may need different privileges and roles. Azure app roles can be mapped to Oracle Database global roles. Azure AD users who are assigned to the app role or are a member of an Azure AD group that is assigned to the app role will be granted the Oracle Database global role when they access the database.
The following diagram illustrates the different types of assignments and mappings that are available.
Figure 5-1 Assignments and Mappings Between Azure AD and Oracle Database
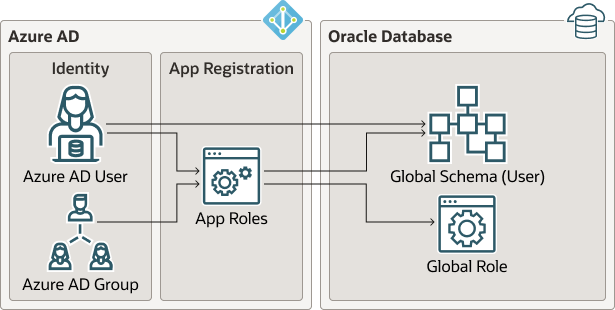
These mappings are as follows:
- An Azure AD user can be mapped directly to an Oracle Database global schema (user).
- An Azure AD user, Azure AD group, or application is assigned to an app role, which is then mapped to either an Oracle Database global schema (user) or a global role.
Use Cases for Connecting to an Oracle Database Using Azure AD
Oracle Database supports four types of use cases for connecting to an Oracle Database instance using Microsoft Azure Active Directory.
- Connection using OAuth 2.0 authorization flow: The client directs the resource owner to an authorization server, which in turn directs the resource owner back to the client with the authorization code. See the Microsoft Azure article Microsoft identity platform and OAuth 2.0 authorization code flow.
- Connection using the resource owner password credentials: The resource owner password credentials (that is, the user name and password) can be used directly to obtain an access token. Azure AD requires an additional client Id and a secret for this flow. (The secret is not required for public client.) See the Microsoft Azure article Microsoft identity platform and OAuth 2.0 Resource Owner Password Credentials.
- Connection using the client credentials: The client acts on its own behalf (the client is also the resource owner) or requests access to protected resources based on an authorization arranged with the authorization server. This flow is used to get the Azure
OAuth2access token for the service principal. An application can also request an Azure ADOAuth2access token directly from Azure AD and pass it through a database client API. See the Microsoft Azure article Get Azure AD tokens by using a service principal. - Connection using on-behalf-of (OBO) token: An Azure application requests an OBO token for a logged in user. The OBO token will also be an access token for the database with the Azure AD user identity and assigned app roles for the database. This enables the Azure AD user to log in to the database as the user and not the application. Only an application can request an OBO token for its Azure AD user and pass it to the database client through the API.
General Process of Integrating Microsoft Azure AD with Oracle Exadata Database Service on Dedicated Infrastructure
Both the Oracle and the Microsoft Azure administrators play roles in configuring the connection between Oracle Exadata Database Service on Dedicated Infrastructure and Microsoft Azure AD.
The general process is as follows:
- The Oracle administrator ensures that the Oracle Database environment meets the requirements for the Microsoft Azure AD integration. See Oracle Database Requirements for the Microsoft Azure AD Integration.
- The Oracle administrator registers the database instance with the Microsoft Azure AD tenancy and then enables the connection between the Oracle Exadata Database Service on
Dedicated Infrastructure and the Azure AD endpoint.
As part of the registration process, the Oracle administrator or the Azure administrator creates or designates Azure app roles to be used for the mappings between the Oracle database and the Microsoft Azure endpoint.
- The Oracle administrator creates and maps global schemas to either an Azure AD user (exclusive schema mapping) or to an Azure app role (shared schema mapping). The Azure AD user or application must be mapped to one schema.
- Optionally, the Oracle administrator creates and maps global Oracle Database roles to Azure app roles.
- The Azure AD end user who wants to connect with the Oracle Exadata Database Service on
Dedicated Infrastructure instance registers the client application as an Azure AD client (similar to how the Oracle database is registered).
The Azure AD client will have a client identification and a client secret, unless the application client is public. If the application client is public, then only the application client identification is necessary.
- The Azure AD end user (who can be a database administrator) connects using an utility such as PowerShell or the Azure command-line interface to retrieve the token and store it in a local file directory. An application can also request an Azure AD
OAuth2access token directly from Azure AD and pass it through a database client API. Refer to the following Oracle Database client documentation for information about passing Azure ADOAuth2tokens:- JDBC-thin clients: Oracle Database JDBC Developer’s Guide
- Oracle Call Interface (OCI): Oracle Call Interface Developer's Guide
- Oracle Data Provider for .NET (ODP): Oracle Data Provider for .NET Developer's Guide.Connecting to Oracle Database
- Once connected to the Oracle Exadata Database Service on Dedicated Infrastructure instance, the Azure AD end user performs tasks as needed.
Configuring the Oracle Database for Microsoft Azure AD Integration
The Microsoft Azure AD integration with the Oracle Database instance requires the database to be registered with Azure AD so that the database can request the Azure AD public key.
- Prerequisites for Azure AD Authentication
Before using Azure AD authentication on databases in the Exadata Cloud Infrastructure, you must use the Networking service to add a service gateway, a route rule, and an egress security rule to the Virtual Cloud Network (VCN) and subnets where your database resources reside. - Configure TLS to Use Azure AD tokens
When sending Azure AD tokens from the database client to the database server, a TLS connection must be established. The TLS wallet with the database certificate for the ExaDB-D service instance must be stored under theWALLET_ROOTlocation. Create atlsdirectory so it looks like:WALLET_ROOT/<PDB GUID>/tls. - Oracle Database Requirements for the Microsoft Azure AD Integration
Before you can configure an Oracle Database instance with Microsoft Azure AD, you must ensure that your environment meets special requirements. - Registering the Oracle Database Instance with a Microsoft Azure AD Tenancy
A user with administrator privileges uses Microsoft Azure AD to register the Oracle Database instance with the Microsoft Azure AD tenancy. - Enabling Microsoft Entra ID v2 Access Tokens
To enable the Microsoft Entra ID v2 access token, you must configure it to use theupnattribute from the Azure portal. - Testing the Accessibility of the Azure Endpoint
You must ensure that your Oracle Database instance can access the Azure AD endpoint. - Managing App Roles in Microsoft Entra ID
In Entra ID, you can create and manage app roles that will be assigned to Azure users and groups and also be mapped to Oracle Database global schemas and roles. - Enabling Azure AD External Authentication for Oracle Database
You can enable a Microsoft Azure AD external authentication with Oracle Database. - Disabling Azure AD External Authentication for Oracle Database
To disable Azure AD External authentication for an Oracle Database instance, you must set parameters with theALTER SYSTEMstatement.
Prerequisites for Azure AD Authentication
Before using Azure AD authentication on databases in the Exadata Cloud Infrastructure, you must use the Networking service to add a service gateway, a route rule, and an egress security rule to the Virtual Cloud Network (VCN) and subnets where your database resources reside.
- Create a service gateway in the VCN where your database resources reside by following the instructions in Task 1: Create the service gateway in OCI documentation.
- After creating the service gateway, add a route rule and an egress
security rule to each subnet (in the VCN) where the database resources reside so
that these resources can use the gateway to use Azure AD authentication:
- Go to the Subnet Details page for the subnet.
- In the Subnet Information tab, click the name of the subnet's Route Table to display its Route Table Details page.
- In the table of existing Route Rules, check whether there is
already a rule with the following characteristics:
- Destination: 0.0.0.0/0
- Target Type: NAT Gateway
- Target: The name of the NAT gateway you just created in the VCN
If such a rule does not exist, click Add Route Rules and add a route rule with these characteristics.
- Return to the Subnet Details page for the subnet.
- In the subnet's Security Lists table, click the name of the subnet's security list to display its Security List Details page.
- In the side menu, under Resources, click Egress Rules.
- In the table of existing Egress Rules, check whether there is
already a rule with the following characteristics:
- Destination Type: CIDR
- Destination: 0.0.0.0/0
- IP Protocol: TCP
- Source Port Range: 443
- Destination Port Range: All
- If such a rule does not exist, click Add Egress Rules and add an egress rule with these characteristics.
Related Topics
Configure TLS to Use Azure AD tokens
When sending Azure AD tokens from the database client to the database
server, a TLS connection must be established. The TLS wallet with the database certificate
for the ExaDB-D service instance must be stored under the WALLET_ROOT
location. Create a tls directory so it looks like:
WALLET_ROOT/<PDB GUID>/tls.
When configuring TLS between the database client and server there are several options to consider.
- Using a self-signed database server certificate vs a database server certificate signed by a commonly known certificate authority
- One-way TLS (TLS) vs Mutual or two-way TLS (mTLS)
- Client with or without a wallet
Self-Signed Certificate
Using a self-signed certificate is a common practice for internally facing IT resources since you can create these yourself and it's free. The resource (in our case, the database server) will have a self-signed certificate to authenticate itself to the database client. The self-signed certificate and root certificate will be stored in the database server wallet. For the database client to be able to recognize the database server certificate, a copy of the root certificate will also be needed on the client. This self-created root certificate can be stored in a client-side wallet or installed in the client system default certificate store (Windows and Linux only). When the session is established, the database client will check to see that the certificate sent over by the database server has been signed by the same root certificate.
A Well-Known Certificate Authority
Using a commonly known root certificate authority has some advantages in that the root certificate is most likely already stored in the client system default certificate store. There is no extra step for the client to store the root certificate if it is a common root certificate. The disadvantage is that this normally has a cost associated with it.
One-Way TLS
In the standard TLS session, only the server provides a certificate to the client to authenticate itself. The client doesn't need to have a separate client certificate to authenticate itself to the server (similar to how HTTPS sessions are established). While the database requires a wallet to store the server certificate, the only thing the client needs to have is the root certificate used to sign the server certificate.
Two-Way TLS (also called Mutual TLS, mTLS)
In mTLS, both the client and server have identity certificates that are presented to each other. In most cases, the same root certificate will have signed both of these certificates so the same root certificate can be used with the database server and client to authenticate the other certificate. mTLS is sometimes used to authenticate the user since the user identity is authenticated by the database server through the certificate. This is not necessary for passing IAM tokens but can be used when passing IAM tokens.
Client with a Wallet
A client wallet is mandatory when using mTLS to store the client certificate. However, the root certificate can be stored either in the same wallet or in the system default certificate store.
A Client without a Wallet
Clients can be configured without a wallet when using TLS under these conditions: 1) One-way TLS is being configured where the client does not have its own certificate and 2) the root certificate that signed the database server certificate is stored in the system default certificate store. The root certificate would most likely already be there if the server certificate is signed by a common certificate authority. If it's a self-signed certificate, then the root certificate would need to be installed in the system default certificate store to avoid using a client wallet.
For details on how to configure TLS between the database client and database server including the options described above, see Configuring Transport Layer Security Authentication in the Oracle Database Security Guide.
If you choose to use self-signed certificates and for additional wallet related tasks, see Managing Public Key Infrastructure (PKI) Elements in the Oracle Database Security Guide.
Oracle Database Requirements for the Microsoft Azure AD Integration
Before you can configure an Oracle Database instance with Microsoft Azure AD, you must ensure that your environment meets special requirements.
- The ExaCS Database to be version 19.17 or higher.
- Connectivity to the database using TLS. Non TLS connections are not supported.
- Outbound network connectivity to Azure AD so that the database can request the Azure AD public key.
- The ExaDB-D Database to be registered with Azure AD.
Note the following:
- The Oracle Database server must be able to request the Azure AD public key. Depending on the enterprise network connectivity setup, you may need to configure a proxy setting.
- Users and applications that need to request an Azure AD token must also be able to have network connectivity to Azure AD. You may need to configure a proxy setting for the connection.
- You must configure Transport Layer Security (TLS) between the Oracle Database client and the Oracle Database server so that the token can be transported securely. This TLS connection can be either one-way or mutual.
- You can create the TLS server certificate to be self-signed or be signed by a well known certificate authority. The advantage of using a certificate that is signed by a well known Certificate Authority (CA) is that the database client can use the system default certificate store to validate the Oracle Database server certificate instead of having to create and maintain a local wallet with the root certificate. Note that this applies to Linux and Windows clients only.
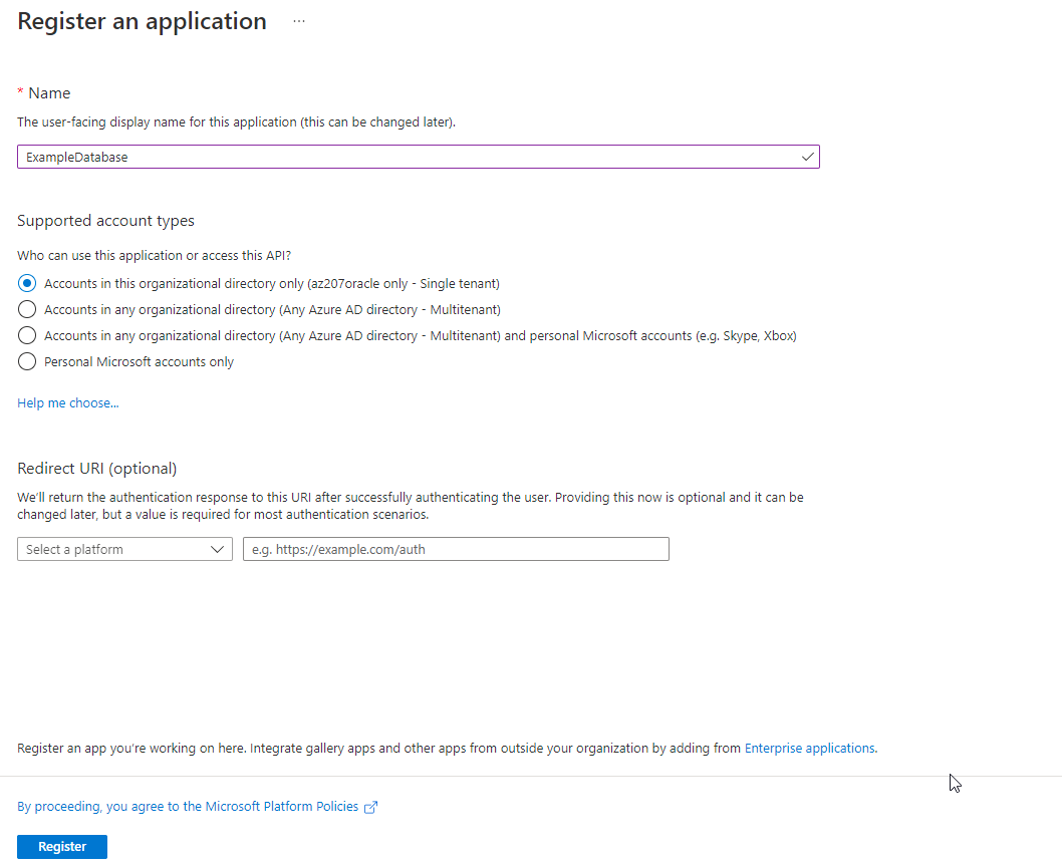
Registering the Oracle Database Instance with a Microsoft Azure AD Tenancy
A user with administrator privileges uses Microsoft Azure AD to register the Oracle Database instance with the Microsoft Azure AD tenancy.
Enabling Microsoft Entra ID v2 Access Tokens
To enable the Microsoft Entra ID v2 access token, you must configure it to use the upn attribute from the Azure portal.
- Check the version of the Entra ID access token that you are using.
- Log in to the Microsoft Entra ID portal.
- Search for and select Entra ID.
- Under Manage, select App registrations.
- Choose the application for which you want to configure optional claims based on your scenario and desired outcome.
- Under Manage, select Token configuration.
- Click Add optional claim and select upn.
- Checking the Entra ID Access Token Version
You can check the version of the Entra ID access token that your site uses by using the JSON Web Tokens web site.
Related Topics
Checking the Entra ID Access Token Version
You can check the version of the Entra ID access token that your site uses by using the JSON Web Tokens web site.
Related Topics
Parent topic: Enabling Microsoft Entra ID v2 Access Tokens
Testing the Accessibility of the Azure Endpoint
You must ensure that your Oracle Database instance can access the Azure AD endpoint.
For an Oracle database to accept Azure AD OAuth2 tokens, the database must request the public key from the Azure AD endpoint.
- Run the following test to determine if the database can connect with the Azure AD endpoint:
SET SERVEROUTPUT ON SIZE 40000 DECLARE req UTL_HTTP.REQ; resp UTL_HTTP.RESP; BEGIN UTL_HTTP.SET_WALLET(path => 'system:'); req := UTL_HTTP.BEGIN_REQUEST('https://login.windows.net/common/discovery/keys'); resp := UTL_HTTP.GET_RESPONSE(req); DBMS_OUTPUT.PUT_LINE('HTTP response status code: ' || resp.status_code); UTL_HTTP.END_RESPONSE(resp); END; /If this test is successful, then a PL/SQL procedure successfully completed message appears.
If the following messages appear, then it means that a database network access control list (ACL) policy blocked your test and you will need to temporarily set an access control list policy to allow you to test this:ORA-29273: HTTP request failed ORA-24247: network access denied by access control list (ACL)- Set the ACL as follows:
BEGIN DBMS_NETWORK_ACL_ADMIN.APPEND_HOST_ACE( host => '*', ace => xs$ace_type(privilege_list => xs$name_list('connect'), principal_name => 'username_placeholder', principal_type => xs_acl.ptype_db)); END; /Replaceusername_placeholderwith the user name of the database user who is running the test. For example:BEGIN DBMS_NETWORK_ACL_ADMIN.APPEND_HOST_ACE( host => '*', ace => xs$ace_type(privilege_list => xs$name_list('connect'), principal_name => 'DBA_DEBRA', principal_type => xs_acl.ptype_db)); END; / - Try running the test again.
- Remove the ACL, because you now no longer need it. For example, assuming your user name is
dba_debra:BEGIN DBMS_NETWORK_ACL_ADMIN.REMOVE_HOST_ACE( host => '*', ace => xs$ace_type(privilege_list => xs$name_list('connect'), principal_name => 'DBA_DEBRA', principal_type => xs_acl.ptype_db)); END; /
- Set the ACL as follows:
If the database cannot connect with the Azure AD endpoint, even after you set the ACL policy, you will most likely need to set the HTTP_PROXY package for your database. Review the topics listed in Related Topics, depending if you are using a default Oracle Database environment or an Oracle Real Application Clusters RAC environment. Your network administrator should be able to tell you what the correct HTTP_PROXY setting should be.
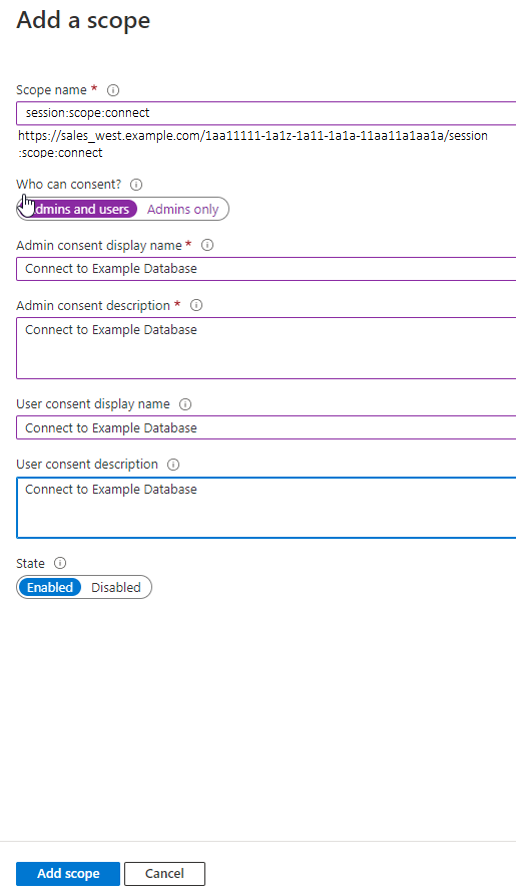
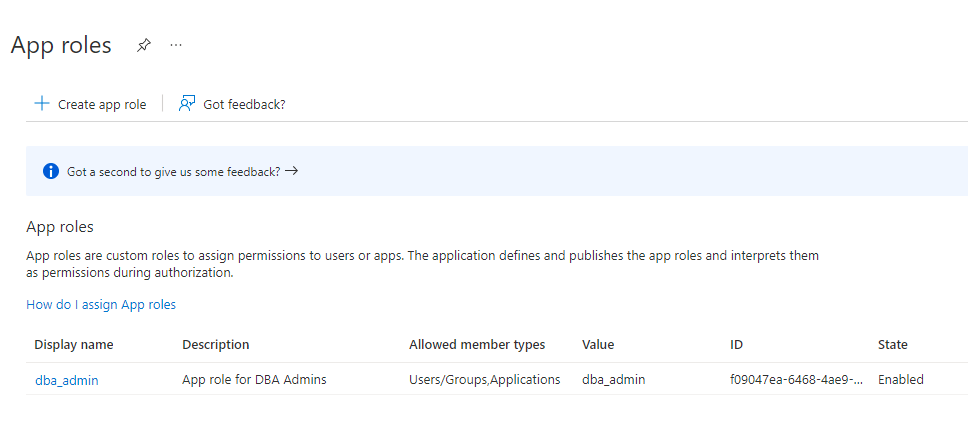
Managing App Roles in Microsoft Entra ID
In Entra ID, you can create and manage app roles that will be assigned to Azure users and groups and also be mapped to Oracle Database global schemas and roles.
- Creating a Microsoft Azure AD App Role
Azure AD users, groups, and applications will be assigned to the app roles. - Assigning Users and Groups to the Microsoft Azure AD App Role
Before Microsoft Azure AD users can have access to the Oracle Database instance, they must first be assigned to the app roles that will be mapped to Oracle Database schema users or roles. - Assigning an Application to an App Role
You can assign an Azure AD client application to a app role.
Creating a Microsoft Azure AD App Role
Azure AD users, groups, and applications will be assigned to the app roles.
Parent topic: Managing App Roles in Microsoft Entra ID
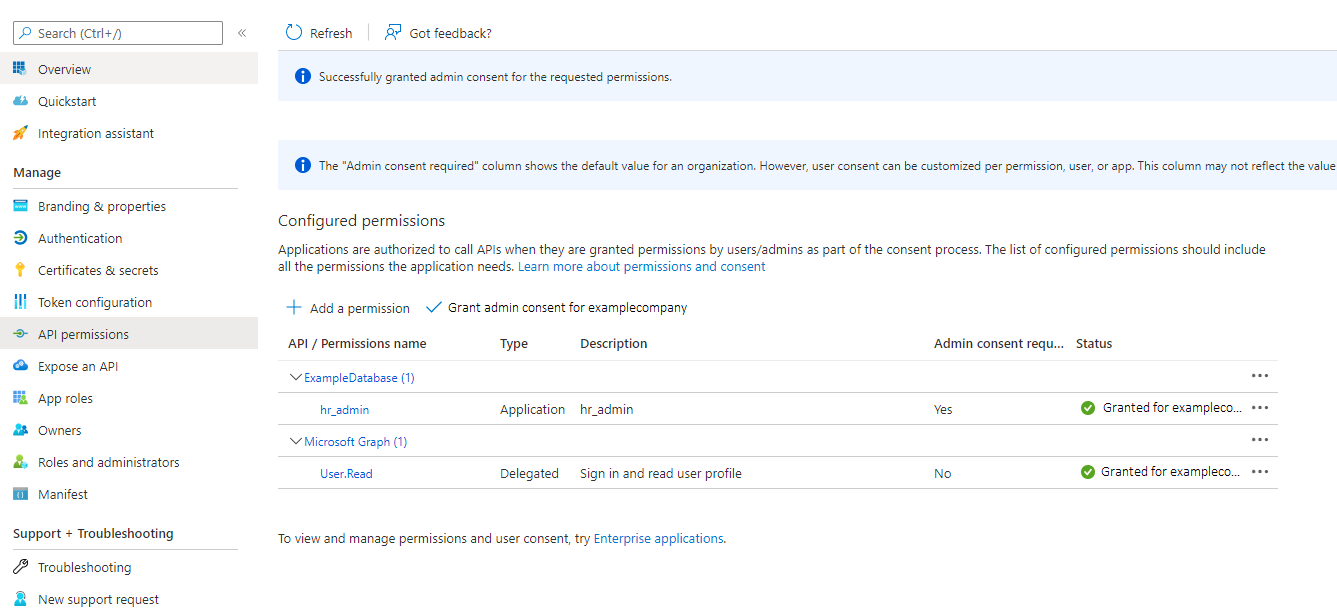
Assigning Users and Groups to the Microsoft Azure AD App Role
Before Microsoft Azure AD users can have access to the Oracle Database instance, they must first be assigned to the app roles that will be mapped to Oracle Database schema users or roles.
- Log in to Azure AD as an administrator who has privileges for assigning Azure AD users and groups to app roles.
- In Enterprise applications, access the Oracle Database application that you registered.
- Use the Directory + subscription filter to locate the Azure Active Directory tenant that contains the Oracle connection.
- Select Azure Active Directory.
- Under Manage, select Enterprise applications, and then select the Oracle Database application name that you registered earlier.
- Under Getting Started, select Assign users and groups.
- Select Add user/group.
- In the Add assignment window, select Users and groups to display a list of users and security groups.
- From this list, select the users and groups that you want to add to the app role, and then click Select.
- In the Add assignment window, select Select a role to display a list of the app roles that you have created.
- Select the app role and then select Select.
- Click Assign.
Parent topic: Managing App Roles in Microsoft Entra ID
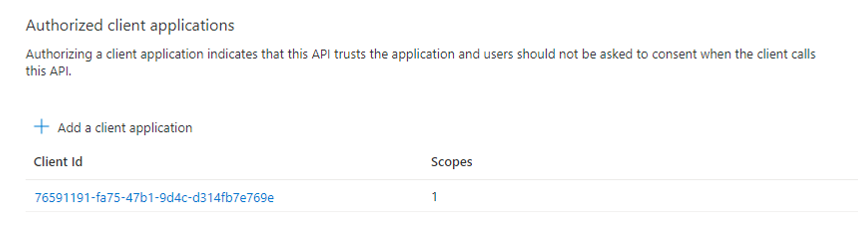
Assigning an Application to an App Role
You can assign an Azure AD client application to a app role.
Related Topics
Parent topic: Managing App Roles in Microsoft Entra ID
Enabling Azure AD External Authentication for Oracle Database
You can enable a Microsoft Azure AD external authentication with Oracle Database.
Mapping Oracle Database Schemas and Roles
Azure AD users will be mapped to one database schema and optionally to one or more database roles.
- Exclusively Mapping an Oracle Database Schema to a Microsoft Azure AD User
You can exclusively map an Oracle Database schema to a Microsoft Azure AD user. - Mapping a Shared Oracle Schema to an App Role
In this mapping, an Oracle schema is mapped to an app role. - Mapping an Oracle Database Global Role to an App Role
Oracle Database global roles that are mapped to Azure app roles give Azure users and applications additional privileges and roles above those that they have been granted through their login schemas.
Exclusively Mapping an Oracle Database Schema to a Microsoft Azure AD User
You can exclusively map an Oracle Database schema to a Microsoft Azure AD user.
Parent topic: Mapping Oracle Database Schemas and Roles
Mapping a Shared Oracle Schema to an App Role
In this mapping, an Oracle schema is mapped to an app role.
Parent topic: Mapping Oracle Database Schemas and Roles
Mapping an Oracle Database Global Role to an App Role
Oracle Database global roles that are mapped to Azure app roles give Azure users and applications additional privileges and roles above those that they have been granted through their login schemas.
Parent topic: Mapping Oracle Database Schemas and Roles
Configuring Azure AD Client Connections to the Oracle Database
You can configure client connections to connect with the Azure AD registered database
- About Configuring Client Connections to Azure ADs
There are numerous ways that you can configure a client to connect with an Oracle Database instance using Azure AD tokens. - Supported Client Drivers for Azure AD Connections
Oracle Database supports several types of client drivers for Azure AD connections. - Operational Flow for SQL*Plus Client Connection in PowerShell to Oracle Database
The connection between the Azure user, Azure AD, and the Oracle Database instance relies on the passing of theOAuth2token throughout these components. - Registering a Client with Azure AD Application Registration
This type of registration is similar to registering Oracle Database with Azure AD app registration. - Examples of Retrieving Azure AD OAuth2 Tokens
These examples show different ways that you can retrieve Azure ADOAuth2tokens. - Configuring SQL*Plus for Azure AD Access Tokens
You must configure SQL*Plus to retrieve the Azure AD database access token from a location and use it when the/slash login is used.
About Configuring Client Connections to Azure ADs
There are numerous ways that you can configure a client to connect with an Oracle Database instance using Azure AD tokens.
You should choose the client connection method that works best with your environment. This guide provides examples of connecting SQL*Plus with different methods of getting an Azure AD OAuth2 access token. All Oracle Database clients version 19.16 and above can accept a token that is passed as a file. The JDBC-thin, Instant Client, and ODP.net drivers also accept the token through the database client API from an application. Oracle Database tools such as SQL*Plus cannot retrieve the tokens directly, so tools such as PowerShell or Azure CLI must be used to retrieve the Azure AD OAuth2 access token. To retrieve an Azure AD token, the client must be registered through the Azure AD app registration process. Registering the client is similar to registering the Oracle Database server with Azure AD using app registration. Both the database and client must be registered with Azure AD.
The database must be registered so the client can get permission to get an access token for the database. The client must be registered so that Azure AD can recognize a trusted client is asking for an access token.
See the following Microsoft Azure articles for more information about connecting clients to Azure AD:
- Quickstart: Configure a client application to access a web API
- Choose the right Azure command-line tool
- Get Azure AD tokens by using the Microsoft Authentication Library
- Install the Azure CLI on Linux
Supported Client Drivers for Azure AD Connections
Oracle Database supports several types of client drivers for Azure AD connections.
- JDBC-thin: Oracle Database 19.16 (July 2022), Oracle Database 21.8 (October 2022)
- OCI (C driver): Oracle Database 19.16 (July 2022)
- Oracle Instant Client based on OCI
- Oracle Data Provider (core): Oracle Database 19.16, Oracle Database 21.7
- Oracle Data Provider (unmanaged): based on OCI
- Oracle Data Provider (managed): Oracle Database 19.16, Oracle Database 21.7
- All other drivers built on OCI adopts the OCI compatibility
Operational Flow for SQL*Plus Client Connection in PowerShell to Oracle Database
The connection between the Azure user, Azure AD, and the Oracle Database instance relies on the passing of the OAuth2 token throughout these components.
This example shows the use of the Resource Owner Password Credential (ROPC) flow with a public client. See the Microsoft Azure article Microsoft identity platform and OAuth 2.0 Resource Owner Password Credentials for detailed information about ROPC.
Figure 5-2 ROPC Operational Flow with a Public Client
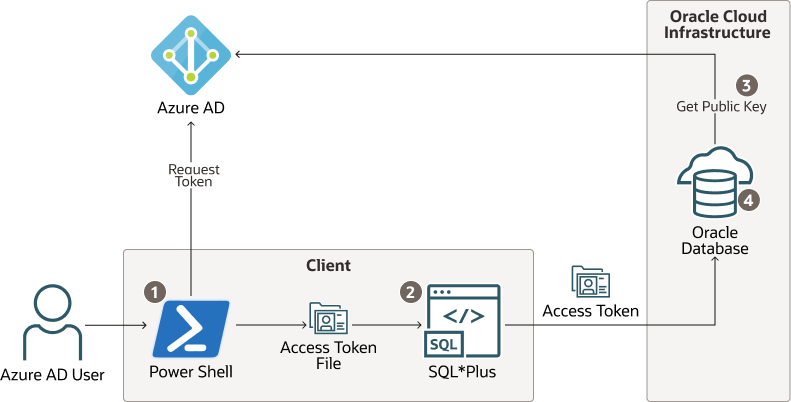
- The Azure user requests an Azure AD access token for the database in PowerShell and the returned token is written into a file called
tokenat a file location. - The Azure user connects to the database using
/slash login. Either thesqlnet.oraortnsnames.oraconnection string tells the instant client that an Azure ADOAuth2token is needed and to retrieve it from a specified file location. The access token is sent to the database. - The database verifies that the access token came from Azure AD (using the Azure AD public key) and then checks the token for additional claims.
- The database finds the schema mapping (exclusive or shared) and creates the session. The database will also grant any global roles that the Azure user is also assigned to through an app role.
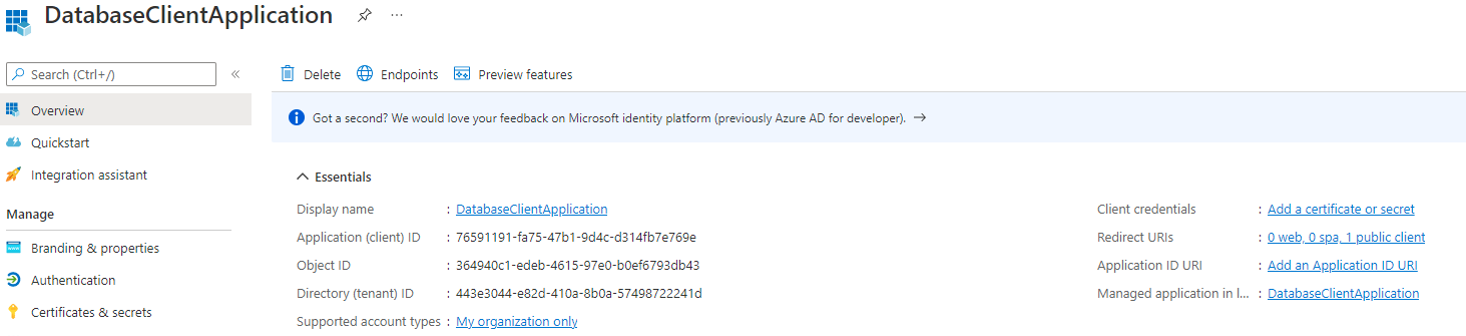
Registering a Client with Azure AD Application Registration
This type of registration is similar to registering Oracle Database with Azure AD app registration.
- Confidential and Public Client Registration
You can register the database client with Azure as either confidential or public depending on your use case. - Registering a Database Client App with Azure AD
Creating the client app registration is similar to creating the Oracle Database instance with the Microsoft Azure AD tenancy.
Confidential and Public Client Registration
You can register the database client with Azure as either confidential or public depending on your use case.
See the Microsoft Azure article Authentication flows and application scenarios for detailed information about authentication flows and application scenarios.
Registering a confidential client app requires that the client have a secret, in addition to the client ID. The confidential client app uses both the client ID and the secret when it makes Azure AD requests. However, in an enterprise, it is not practical for every SQL*Plus and SQLcl user to create a separate app registration with its own secret. In addition, a secret is no longer a secret when you start to share it within an organization. It is far better to just create a public client app. A public client app does not have a secret; it only has a client ID. All database tool users can use the public client ID when they connect to Azure AD to get an access token. The Azure AD user still needs to authenticate to Azure AD with their own user credential.
Examples of Retrieving Azure AD OAuth2 Tokens
These examples show different ways that you can retrieve Azure AD OAuth2 tokens.
- Example: Using PowerShell to Get a Token Using Resource Owner Password Credentials
This example shows how to use PowerShell to get an Azure AD access token by using Resource Owner Password Credentials (ROPC). - Example: Using Python with Microsoft Authentication Library Using an Authorization Flow
Because this example with the Microsoft Authentication Library (MSAL) is in Python, it can be run on a variety of platforms such as PowerShell and Linux. - Example: Using Curl with a Resource Owner Password Credential Flow
This example shows how to use thecurlcommand against the Azure AD API uses a Resource Owner Password Credential (ROPC) flow with a public Azure AD client. - Example: Azure CLI Using Authorization Flow
This example shows how to use the Azure CLI to retrieve an access token and then write the token to a file.
Example: Using PowerShell to Get a Token Using Resource Owner Password Credentials
This example shows how to use PowerShell to get an Azure AD access token by using Resource Owner Password Credentials (ROPC).
OAuth2 access token by making a REST call from PowerShell. This configuration requires several values that were generated or that you specified when you registered the Oracle Database instance with Azure AD.
OAuth2 access token has been retrieved and stored as a file. The next step is to enable the SQL*Plus client to use the store access token and send it to the database.
Parent topic: Examples of Retrieving Azure AD OAuth2 Tokens
Example: Using Python with Microsoft Authentication Library Using an Authorization Flow
Because this example with the Microsoft Authentication Library (MSAL) is in Python, it can be run on a variety of platforms such as PowerShell and Linux.
OAuth2 authorization flow is necessary for a user to add the second authentication. Because the authorization flow requires two round trips to Azure AD, it is best handled using the MSAL. See the Microsoft article Get Azure AD tokens by using the Microsoft Authentication Library for how to use a python script with MSAL. These instructions are for the Databricks service, but the scope is changed to the database App ID URI and scope instead of the Databricks scope.
Parent topic: Examples of Retrieving Azure AD OAuth2 Tokens
Example: Using Curl with a Resource Owner Password Credential Flow
This example shows how to use the curl command against the Azure AD API uses a Resource Owner Password Credential (ROPC) flow with a public Azure AD client.
Parent topic: Examples of Retrieving Azure AD OAuth2 Tokens
Example: Azure CLI Using Authorization Flow
This example shows how to use the Azure CLI to retrieve an access token and then write the token to a file.
Parent topic: Examples of Retrieving Azure AD OAuth2 Tokens
Configuring SQL*Plus for Azure AD Access Tokens
You must configure SQL*Plus to retrieve the Azure AD database access
token from a location and use it when the / slash login is
used.
You can specify the TOKEN_AUTH and
TOKEN_LOCATION parameters in tnsnames.ora, as
well as in sqlnet.ora. The TOKEN_AUTH and
TOKEN_LOCATION values in the tnsnames.ora
connect strings take precedence over the sqlnet.ora settings for
that connection. For example:
(description=
(retry_count=20)(retry_delay=3)
(address=(protocol=tcps)(port=1522)
(host=example.us-phoenix-1.oraclecloud.com))
(connect_data=(service_name=aaabbbccc_exampledb_high.example.oraclecloud.com))
(security=(ssl_server_cert_dn="CN=example.uscom-east-1.oraclecloud.com,
OU=Oracle BMCS US, O=Example Corporation,
L=Redwood City, ST=California, C=US")
(TOKEN_AUTH=OAUTH)(TOKEN_LOCATION="/test/oracle/aad-token"))After the connect string is updated with the TOKEN_AUTH
and TOKEN_LOCATION parameters, the Azure user can log in to the
Oracle Database instance by running the following command to start SQL*Plus. You can
include the connect descriptor itself or use the name of the descriptor from the
tnsnames.ora file.
connect /@exampledb_highOr the user can use the connect string. For example:
connect /@(description=
(retry_count=20)(retry_delay=3)
(address=(protocol=tcps)(port=1522)
(host=example.us-phoenix-1.oraclecloud.com))
(connect_data=(service_name=aaabbbccc_exampledb_high.example.oraclecloud.com))
(security=(ssl_server_cert_dn="CN=example.uscom-east-1.oraclecloud.com,
OU=Oracle BMCS US, O=Example Corporation,
L=Redwood City, ST=California, C=US") (TOKEN_AUTH=OAUTH)(TOKEN_LOCATION="/test/oracle/aad-token")The database client is already configured to get an Azure
OAuth2 token because TOKEN_AUTH has already
been set, either through the sqlnet.ora file or in a connect
string. The database client gets the OAuth2 token and then sends
the token to the Oracle Database instance.
Trace Files for Troubleshooting Oracle Database Client Connections with Azure AD
You can use trace files to troubleshoot Oracle Database client connections with Azure AD connections.
- About Trace Files Used for Troubleshooting Connections
You can generate two levels of trace files to troubleshoot Microsoft Azure AD connections on client side. - Setting Client Tracing for Token Authentication
You can addEVENTsettings to the client-sidesqlnet.orafile to control client tracing.
About Trace Files Used for Troubleshooting Connections
You can generate two levels of trace files to troubleshoot Microsoft Azure AD connections on client side.
The two levels of trace files that you can generate are as follows:
- Low level tracing prints traces in case of failures:
- If TCPS is not set up for the Azure AD connection, then it prints a message that the protocol has to be TCPS.
- If
SSL_SERVER_DN_MATCHis not set toTRUE, then it prints a message that the value isFALSE. - If
TOKEN_LOCATIONhas not been specified, then it prints a message that the token location does not exist. - If the token is not present at the specified
TOKEN_LOCATION, then it prints a message. - If the application has passed in the token without setting
OCI_ATTR_TOKEN_ISBEARERto true, it prints a message for the missing attribute. - If the application has set
OCI_ATTR_TOKEN_ISBEARERtoTRUEand not passed in the token, it prints a message for the missing attribute. - If the token has expired, then it prints a message.
- High level tracing prints traces in case of failure as mentioned above. In addition, it prints traces in case of success, as follows:
- It prints where
SSL_SERVER_DN_MATCHis present,tnsnames.oraorsqlnet.ora. It also prints the value asTRUEif set toTRUE. - If both the token and
OCI_ATTR_TOKEN_ISBEARER=trueare set by the application, then it prints a message. - If
TOKEN_AUTHhas the correct valueOAUTH, then it prints the value. - If the token is not expired, then it prints a message.
- It prints where